Overview
The study of RHCE will enable the candidates to sit for the certification exam and clear the test successfully. We, the members of AP2V, take great interest in grooming the future of the aspirants and curating for them a roadmap to success.
KEY USPS AND CERTIFICATION DETAIL -
|
1 Gain the idea of how to work with Linux |
The students and aspiring candidates provide knowledge and ideas about the function of CentOS and how to handle Linux workability. |
|
2.learn the framework of RedHat |
We at AP2V allow the aspirants to deal with the subjects and topics of RedHat in detail for clear understanding and comprehension. |
|
3. Enhance their opportunities at work |
Red Hat Certification Online provided at AP2V is recognised by the leading firms which in turn enhances the job opportunities for the candidates. |
Benefits of RHCE Certification Training Online
RHCE CERTIFICATION TRAINING ONLINE- FUNDAMENTALS & KEY FEATURES -
An RHCE expert has the knowledge and insight to solve any query and crisis related to RHCSA and CentOS. He has the potential to solve the problems on the platform and provide effective results.
At AP2V, we are highly concerned with teaching the students about the practical application of the RHCE Certification Course Online. They are taught to program and configure on the Red Hat and Linux platform using the resources of the institute.
The magnificent and well-mechanized lab facilities also help the students to develop their program and work on the projects and assignments without any problems or hassles. We believe in grooming a prospective future for the students and consider it to be our responsibility to help them move towards their goals.
The experts can freelance on websites and other platforms to develop CentOS environments and utilize Linux for computing. The knowledge of the candidates is massively enhanced when they are enrolled on AP2V organizations for studying Red Hat.
RHCE CERTIFICATION TRAINING ONLINE- COURSE OUTLINE
RHCE Training is essential for cracking the Red Hat certification examination. A thorough study of the topic and discussion of queries and doubts are always appreciated and entertained by the faculty members of AP2V.
They are indeed keen to impart knowledge to the pupils and help them to understand the subject in a better manner. The RHCE Certification Training Online is also available online so that all the individuals who are unable to attend the classes on campus can obtain the benefits of becoming a part of the fraternity from their homes.
The flexible hour of the classroom lectures and the live lectures allow the pupils to manage studies and work simultaneously. The candidates are provided adequate study material so that they do not lack the resources to understand the topics well. The teachers also conduct hackathons and quiz sessions to keep the lectures interesting and the students invested in their course studies.
WHO SHOULD ENROLL IN THIS COURSE?
Students who desire to bag a secure job in the IT field in this competitive era should go for learning the workability of RedHat and the ways to handle Linux. They can understand the basic functioning of the topics and perform well at work to climb the ladders of success and gain promotions.
WHY WILL THIS COURSE CHANGE YOUR CAREER?
The relevant knowledge of RedHat is always beneficial in securing a prestigious post in the IT firms and heading the team for handling computing and processivity. You have also conferred the idea to create a RedHat virtual machine on the Windows platform without any inconvenience. This is certainly a work of expertise and the knowledge of the same can be advantageous to you in many ways.
TOP COMPANIES HIRE CLOUD PRACTITIONER SPECIALISTS
Our institute is recognized by the world's best IT companies and firms. The organization praised the quality of teaching at AP2V and feels proud to be associated with our fraternity. The leading company delegates often interact with our candidates which in turn opens the door of opportunities for the pupils to gain exposure to the job sectors.
Career Opportunities
Why Choose AP2V?
Flexible & Personalized Learning
Experience ultimate flexibility with batch slots, online learning, recorded sessions, backup classes, and easy payment options all designed for your convenience and success
Expert Trainers, Real-World Projects
Learn from globally certified trainers with industry expertise, using innovative training methods and exclusive live project work to ensure deep, practical skills
Career-Driven Skill Building
Get comprehensive career support through technical interview prep, resume workshops, applied project work, personality development, and continuous mentoring to make you job-ready and confident
Trusted Industry Leader
Join a respected institute with over 10 years of excellence, top global certifications, 50+ expert trainers, and consistent high student ratings focused entirely on your growth and future
Lifetime Guidance & Mentorship
Gain ongoing value with lifetime access to class recordings, continuous expert guidance, dedicated mentorship, and more—ensuring you always have support on your learning journey
Your Success, Our Commitment
Our dedicated placement team works for you, and all trainings are certificate-oriented with options for guaranteed certificates
RHCE Certification Training Online Curriculum
Course Content
Industry Project
Training Online Exam & Certification
Live your dream to be hired by top IT Companies with us, offering an array of professional courses with 100% Job Assistance




Trusted By 50,000 people
World Wide
















Student Success Stories
Discover how professionals transformed their careers with AP2V’s expert-led programs.
Cracked Their Dream Careers In
New Batch and Workshop
Join the latest training batches and hands-on workshops designed for real-world IT skills.

Certified Kubernetes Administrator (CKA)

Devops Foundation
Mastering in Python Programming
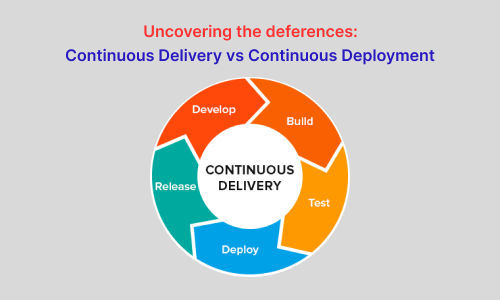
Recent Articles
Explore our latest articles on trending technologies, tools, and real-world IT practices.
Frequently Asked Questions
The certification of RHCE courses cost about two thousand INR in AP2V which is an affordable price for students from different backgrounds.
The RHCE should be able to handle the programming of Linux and control CentOS.
The institute of AP2V is well known for offering the best RedHat course in India.
The RHCE certification trains professionals to opt for better job prospects in the IT industry.
You may take the assistance of VM Virtual Box Manager to establish an RHCE exam lab at home.
After completion of the RedHat course, the candidate can start looking for prospective jobs in the field of computing.
RHCE courses taught at AP2V enable the pupils to thoroughly understand the concepts of Linux and develop the RedHat program on Windows.
The RHCE course focuses on developing the base of the candidate in RedHat computing and software.
The cost of the RHCE exam is within 2000 INR which allows the pupils to easily opt for the course.
To become an RHCE, the individual has to complete the course study and clear the examination.
RHCE certification from reputable institutes like AP2V is a prominent mark of credentials in the resume of the candidate.
The starting salary of an RHCSA professional typically ranges from entry-level to junior system administrator roles, depending on skills, location, and experience.
RHCE Certification is vital in enhancing your knowledge and skills in computing topics and clouds and containers.
As beginners, you may opt for expert help and assistance from trusted institutes like AP2V to prepare for the certification tests.
Recorded Videos
- Enhance students learning Experience.
- Relief the pressure of Note-Taking.
- Lifetime Access.
- Learning Flexibility.
- Easy to retakes of each sessions.
- Pocket friendly course.
Live Interactive Classes
- Lectures bring together diversed group of students to learn in different ways.
- Live interactive Instructor-led training.
- 24 x 7 hours learning assistance.
- Have a team of well-qualified expert trainers.
- Lifetime access of class recordings.
- Affordable fees.
Sign in to your account
Sign in to your account
Welcome back! Login with your data that you entered during registration.
-
-
Email and Password are case sensitive...
- Forget Password
Forget Password
We will send a password reset link on your email.
-
Please enter registered email.
Create Account
Create Account
Use your email for registration.
-
Please enter name
-
Please enter email
-
Please enter password
Must be grater 6 characters as long.
Can contain any letters a to z or A to Z.
Can contain some special characters eg(@,#,$,%,&,*,%).
Can contain any numbers from 0 to 9.